Cyber Security and Cloud Protection
Play All
 0:13:13
0:13:13
Part 8-5 - Configure different policies like Users, Groups, RegEx, and Time in Keycloak Policy
15 Views
10 months ago
cybersecurity
 0:03:41
0:03:41
5 Most Devastating Cyber Attacks | Cybersecurity Insights #18
22 Views
4 years ago
PhD. Le Toan Thang
 0:22:03
0:22:03
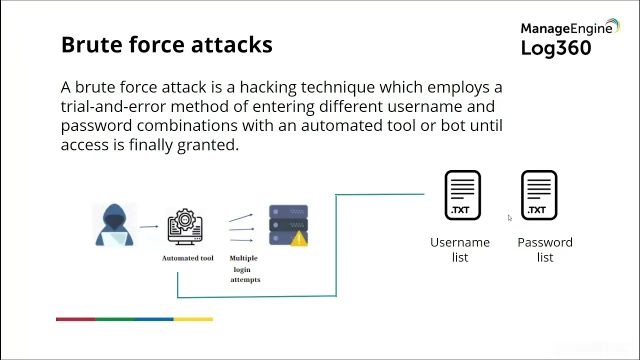
8 Most Common Cybersecurity Threats | Types of Cyber Attacks | Cybersecurity for Beginners | Edureka
27 Views
4 years ago
PhD. Le Toan Thang
 0:21:52
0:21:52
|GravityZone installation - Ubuntu machine |Bit defender |how to manually install GravityZone Part1
17 Views
4 years ago
PhD. Le Toan Thang
 0:33:47
0:33:47
|GravityZone installation - Ubuntu machine |Bit defender |how to manually install GravityZone Part2
21 Views
4 years ago
PhD. Le Toan Thang
 0:00:55
0:00:55
|GravityZone installation - Ubuntu machine |Bit defender |how to manually install GravityZone Part3
25 Views
4 years ago
PhD. Le Toan Thang